Updated: March 17, 2025
It was 3:47 AM when the attack began. Silent. Invisible. Ruthless. It moved at 1ure.3 terabits per second—an unrelenting flood of data packets designed to cripple an entire banking infrastructure within minutes. Security analysts barely had time to react before transaction failures started flooding in, ATM networks ground to a halt, and customer trust began to evaporate. By sunrise, the damage was done—millions lost, reputations shattered.
This wasn’t a plot from a cyber-thriller. It was a real-world event. In July 2023, a massive Distributed Denial-of-Service (DDoS) attack targeted European financial institutions, causing widespread service disruptions. The culprit? A sophisticated, AI-driven botnet that leveraged unprotected endpoints across the globe.
Cyber threats are no longer a nuisance. They pose an existential risk to businesses, economies, and even nation-states. Traditional cybersecurity strategies—patching, firewalls, and endpoint protection—are proving to be mere sandbags against a digital tsunami.
In response, the paradigm is shifting. Secure Networking isn't just an upgrade—it's a fundamental shift in how we defend digital landscapes. Instead of treating security as an add-on, it becomes the backbone of every network interaction, ensuring protection is woven into every data exchange, device connection, and system operation.
For decades, cybersecurity has been built on a castle-and-moat model—fortify the perimeter, keep threats outside. Firewalls, VPNs, and intrusion prevention systems (IPS) formed the first line of defence. But in an era of cloud computing, remote work, and AI-powered cybercrime, this model is passe.
Today’s networks are fluid. Users connect from coffee shops, co-working spaces, and cruise liners. Data flows across multi-cloud environments. Attackers are no longer battering at the front gate; they are already inside—lurking in compromised credentials, exploiting misconfigured APIs, and embedding malicious scripts in everyday applications.
A 2024 report by Cybersecurity Ventures estimates that cybercrime will cost the world $9.5 trillion annually, up from $3 trillion in 2015. The growth is exponential, fuelled by ransomware-as-a-service, nation-state cyber warfare, and the rise of AI-driven attacks.
The solution? Networks that do not merely transmit data but defend it in real time.
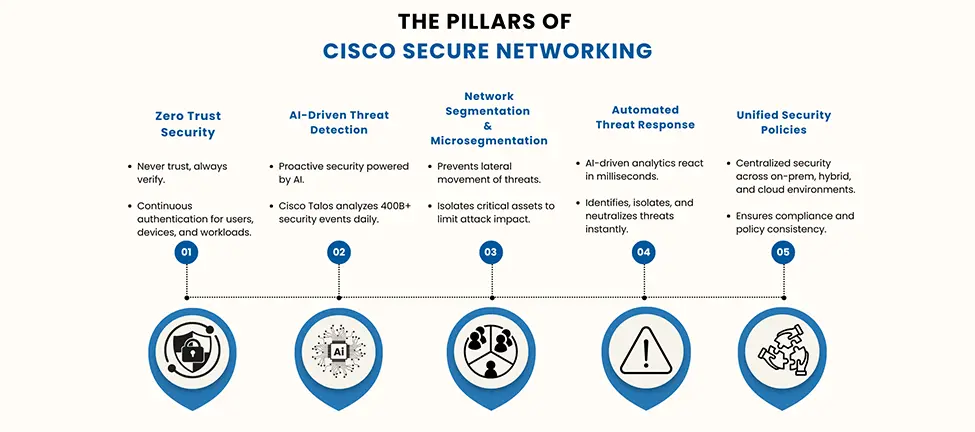
Secure Networking is a transformative approach that integrates security into every aspect of a network. Rather than relying on standalone security solutions bolted onto infrastructure, security is embedded at every layer—edge, core, and cloud.
The shift to Secure Networking is not just an IT decision—it is a strategic necessity in today's cyber-threat landscape. Recent industry reports indicate that the average cost of a data breach has reached $4.45 million, with detection and response times stretching to nearly 277 days.
Step 1: Assess Current Network Security Posture – Conduct a security audit to identify vulnerabilities and gaps in the existing infrastructure.
Step 2: Implement Zero Trust Frameworks – Enforce multi-factor authentication (MFA), identity verification, and microsegmentation.
Step 3: Leverage AI for Threat Detection – Deploy Cisco SecureX to monitor network activity and automate response mechanisms.
Step 4: Automate and Orchestrate Security – Use intent-based networking to dynamically adjust security policies in response to threats.
Step 5: Educate and Train Staff – Human error is responsible for over 85% of security breaches. Security awareness training is critical.
Final Thoughts: Security is No Longer Optional
The digital battleground has changed. Threat actors are no longer lone hackers in dimly lit rooms but well-funded, highly coordinated entities. They are leveraging AI, automation, and advanced persistent threats (APTs) to bypass traditional security measures.
Secure Networking is not a luxury—it is a necessity. By embedding security into the very foundation of network infrastructure, businesses can proactively defend against cyber threats rather than reactively mitigate damage.
The choice is stark: Evolve or be compromised.
Looking to strengthen your organization's cybersecurity posture? Partner with Proactive Data Systems—your trusted ally in Secure Networking. Our expert solutions ensure robust, scalable, and intelligent protection for your business. Contact us today to build a more secure tomorrow.
We'll get back to you shortly.